High-paying affiliate programs 2026 can be advantageous for both novice and seasoned marketers.
Targeting high-paying affiliate offers makes practical sense.
Whether you’re a blogger or an industry expert, the effort to promote a product yielding a $1,000 commission is comparable to promoting one with a $10 payout.
Hence, it’s logical to pursue higher earnings.
Mind you, it takes the same time and effort to promote both products.
However, with numerous niches and a plethora of affiliate marketing programs available, identifying those with optimal returns can feel daunting.
Luckily, I’ve conducted thorough research and curated a list of the best, highest-paying affiliate programs.
High Paying Affiliate Programs
Augusta Precious Metals
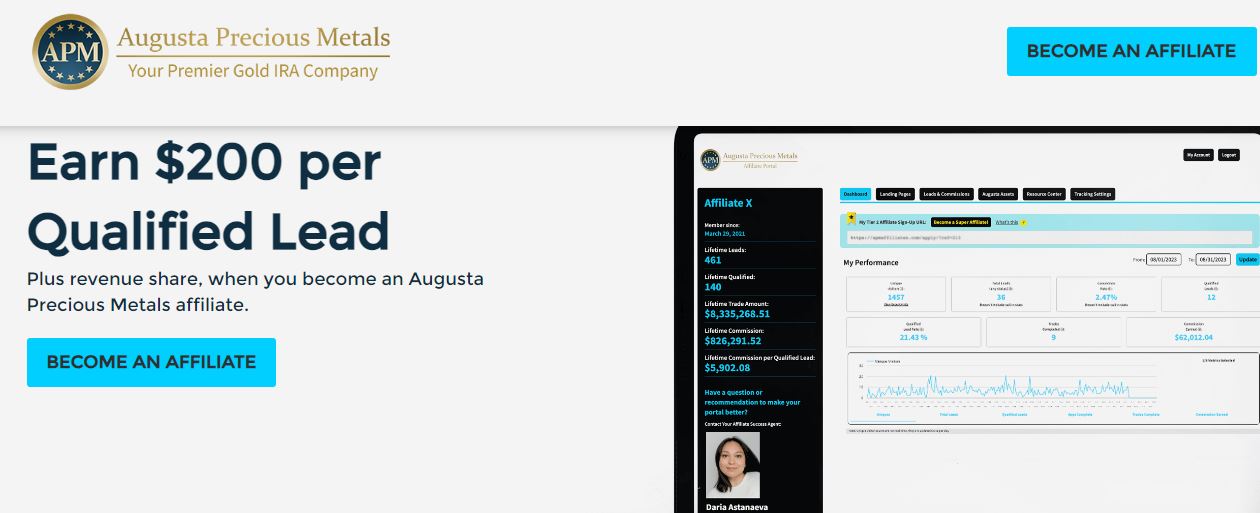 Augusta Precious Metals stands out as a premier provider of gold and silver IRAs, offering investors a strategic way to diversify their retirement portfolios with precious metals.
Augusta Precious Metals stands out as a premier provider of gold and silver IRAs, offering investors a strategic way to diversify their retirement portfolios with precious metals.
As an affiliate, you have the potential to earn up to 10% commission per sale.
With an average transaction value of $200,000, this translates to an impressive $20,000 commission for each sale.
The program also boasts a generous cookie duration of up to 90 days, ensuring you capture more conversions.
Backed by a trusted name in the precious metals industry, Augusta Precious Metals offers a highly profitable opportunity for affiliates targeting investors and retirement planners focused on wealth protection.
- Affiliate Sign-Up URL: apmaffiliates.com
- Commission: 8-10% per trade, $200 for qualified lead.
- Cookie: 90 days
Wealthy Affiliate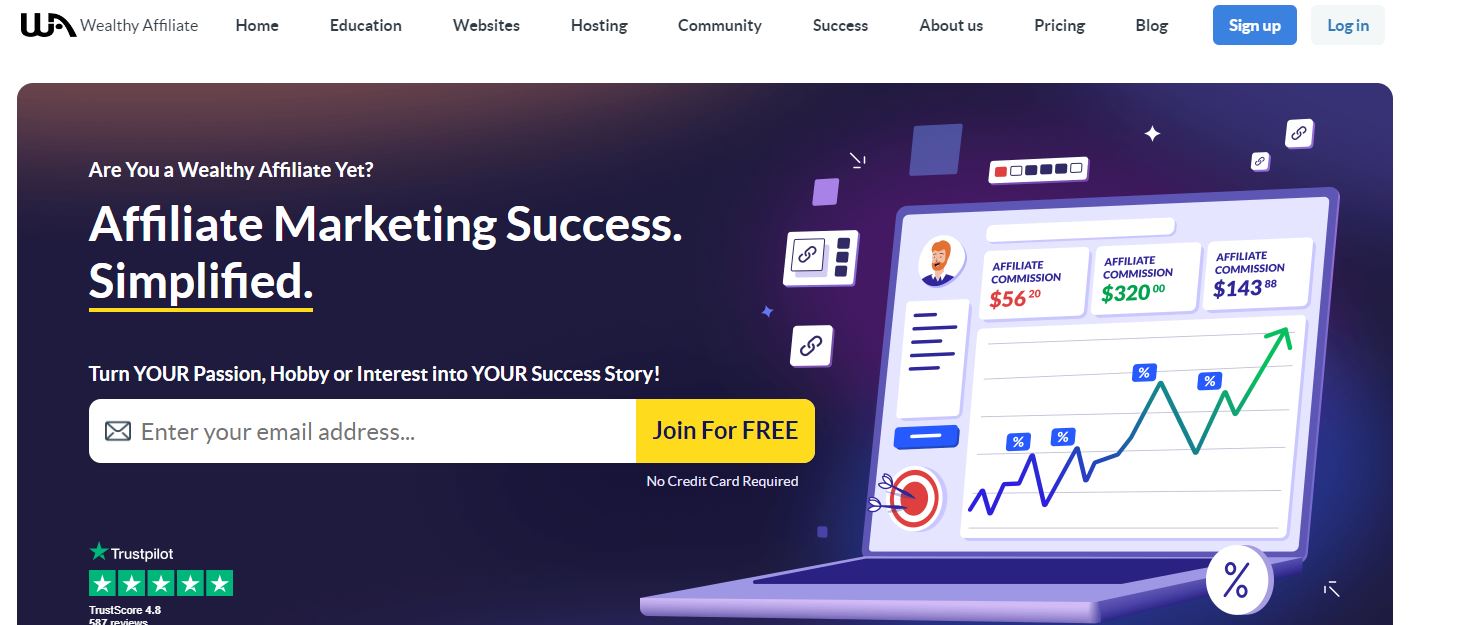
Wealthy Affiliate isn’t just another run-of-the-mill online platform; it’s a powerhouse of resources, tools, and community support designed to empower individuals aspiring to thrive in the digital landscape.
Whether you’re a seasoned marketer or a novice entrepreneur, Wealthy Affiliate offers a robust suite of features tailored to elevate your online presence and maximize your earning potential.
At its core, Wealthy Affiliate provides comprehensive training modules covering every aspect of affiliate marketing, from niche selection to advanced SEO strategies.
With step-by-step tutorials, live webinars, and interactive classrooms, members gain invaluable insights and actionable techniques to propel their online ventures to new heights.
But Wealthy Affiliate goes beyond mere education; it’s a thriving community of like-minded individuals dedicated to mutual growth and success.
Through forums, live chats, and networking events, members can connect, collaborate, and share experiences, fostering a supportive environment conducive to achievement.
Here is the commission breakdown:
- Premium $49 + free domain (first month) => $20
- Premium Plus+ $99 + 2 Free Domains (first month) => $40
- Premium Monthly $49/Month => $23.50 recurring
- Premium Plus+ $99/Month => $46.50 recurring
- Premium Yearly $497/Year=> $230 recurring
- Premium Plus+ $697/Year => $320 recurring
Wealthy Affiliate is a lucrative recurring affiliate program.
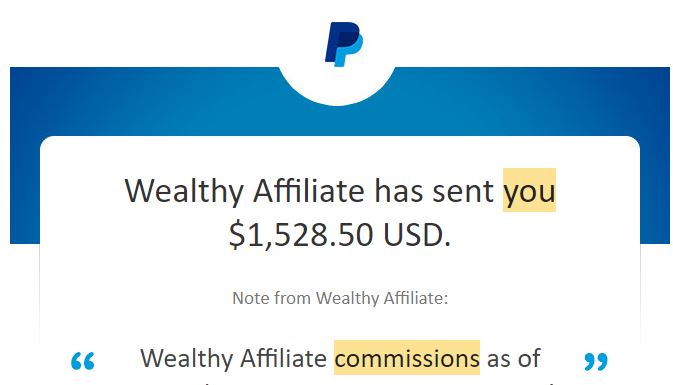
- Wealthy Affiliate Review
- Affiliate Sign-Up URL: Wealthy Affiliate Program
- Commission: 50%
- Cookie: 90 days
Amazing Selling Machine
 Amazing Selling Machine (ASM) is not just another e-commerce course; it’s a comprehensive program designed to equip entrepreneurs with the tools and knowledge needed to thrive in the competitive world of online selling.
Amazing Selling Machine (ASM) is not just another e-commerce course; it’s a comprehensive program designed to equip entrepreneurs with the tools and knowledge needed to thrive in the competitive world of online selling.
ASM offers premium training and resources, reflecting its commitment to excellence.
While the investment may seem substantial at $4,997, it’s important to recognize the unparalleled value it provides in terms of actionable insights, mentorship, and ongoing support.
Affiliate Program:
The ASM affiliate program presents an enticing opportunity for marketers to earn significant commissions by promoting the course.
Affiliates can earn lucrative payouts for each referral, making it an attractive option for those looking to monetize their influence.
With a high-quality product like ASM, affiliates can confidently promote a valuable resource to their audience while earning generous commissions.
- Affiliate Sign-Up URL: Amazing Selling Machine Affiliates
- Commission: Up to $1,500
- Cookie: 90 days
Legendary Marketer
Legendary Marketer is a renowned online education platform that specializes in teaching various aspects of digital marketing and online business.
 Led by industry experts, it offers a diverse range of courses tailored to meet the needs of aspiring entrepreneurs and seasoned professionals alike.
Led by industry experts, it offers a diverse range of courses tailored to meet the needs of aspiring entrepreneurs and seasoned professionals alike.
Legendary Marketer provides an extensive array of courses covering topics such as affiliate marketing, digital advertising, sales strategies, and personal branding.
Whether you’re a beginner looking to kickstart your online business journey or an experienced marketer seeking advanced strategies, Legendary Marketer has something for everyone.
You have to purchase one of the courses to join the affiliate program.
The 15-Seconds Free leads cost only $1 which also gives you an additional course as a bonus.
Try it below
- Affiliate Sign-Up URL: 15 Seconds Free Leads
- Commission: up to $1,000
- Cookie: 90 days
Funnel Freedom 
Freedom Breakthrough is a comprehensive online program designed to empower individuals on their journey to financial freedom and success.
Offering a wealth of knowledge and resources, it equips participants with the tools and strategies needed to achieve their financial goals.
The Funnel Freedom affiliate program provides an excellent opportunity for affiliates to earn generous commissions by promoting the program.
Funnel Freedom provides a transformative opportunity for individuals to break free from financial constraints and achieve their dreams.
Affiliates can leverage the platform’s popularity and credibility to attract referrals, earning substantial commissions for each successful sale.
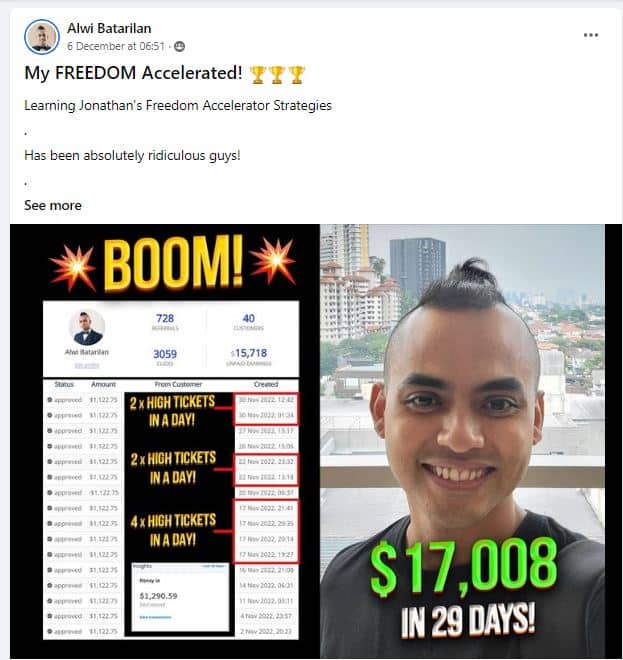
With a well-designed affiliate program, affiliates can unlock significant earning potential while contributing to the financial empowerment of others.
You also have an opportunity to promote 15+ other affiliate programs without leaving your dashboard.
- Affiliate Sign-Up URL: Funnel Freedom Affiliates
- Free Training: 5 Seconds Silent Videos
- Commission: 40%- Up to $1,000 and 10% from your affiliates.
- Cookie: 30 days
Systeme.io

Systeme.io is an all-in-one marketing platform designed to streamline business operations, from sales funnels to email marketing and automation.
With systeme.io, users can easily create and manage their online presence, optimize sales processes, and grow their businesses efficiently.
- Affiliate Sign-Up URL: Systeme.io
- Commission Percentage: up to 60% lifetime commissions.
- Price Points: from $27 to $828
- Cookie Duration: Cookie duration of 30 days.
Systeme.io’s affiliate program provides a lucrative opportunity for individuals and businesses to monetize their networks and earn passive income by promoting a valuable and comprehensive marketing platform.
With high commission rates, competitive pricing, and a generous cookie duration, affiliates can capitalize on the platform’s success while helping others grow their businesses.
ClickFunnels
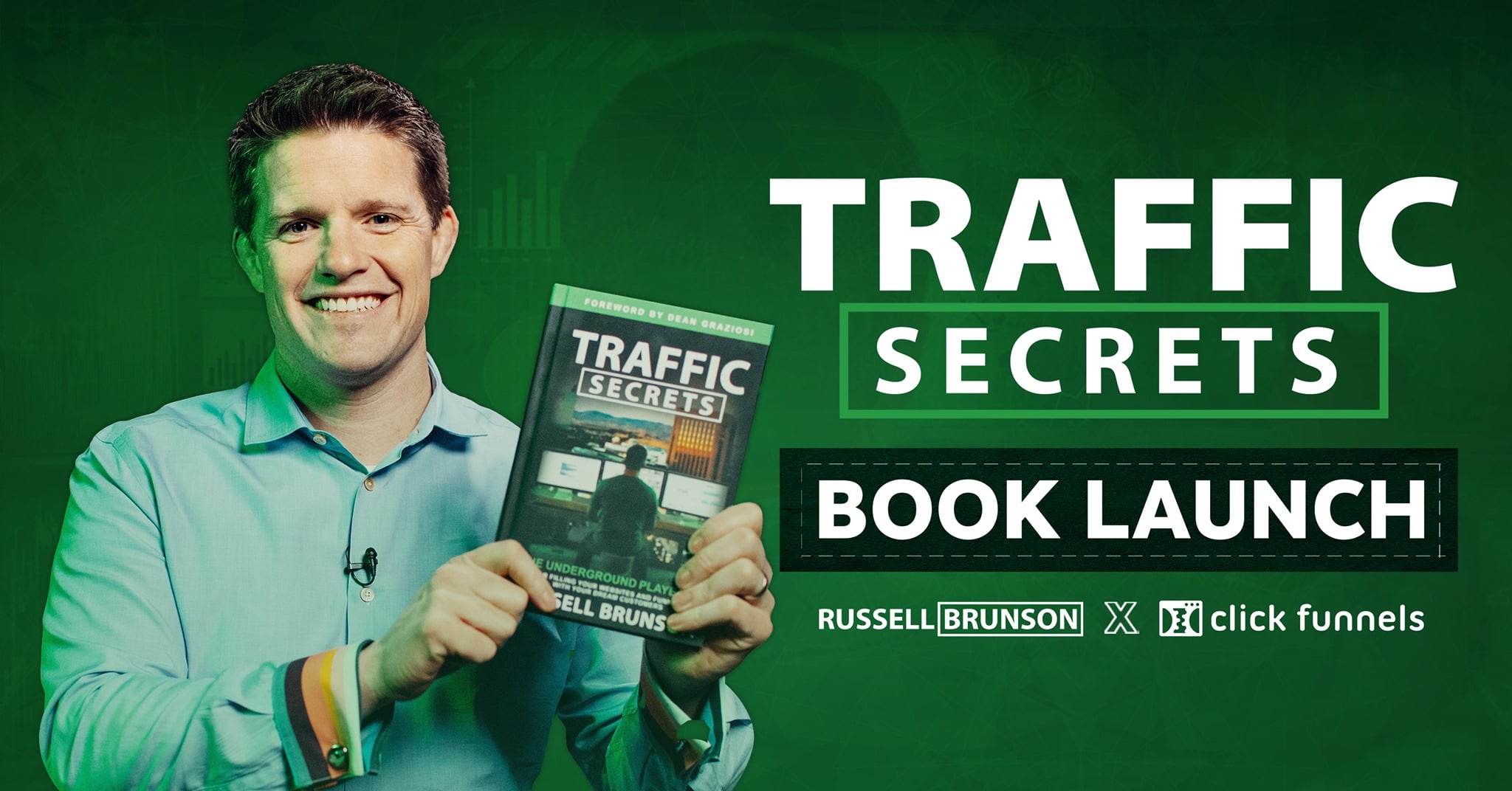
For those venturing into affiliate marketing funnels, the name ClickFunnels is likely familiar.
It’s the brainchild of Russell Brunson, a seasoned figure in the realms of Internet and affiliate marketing.
Primarily, ClickFunnels empowers users to craft effective sales funnels, facilitating the conversion of leads into paying customers.
ClickFunnels stands out for its efficacy in selling high-ticket affiliate products, favoured by numerous email marketing experts.
Comparing this offer to others in this space, affiliates enjoy a 40% recurring monthly commission on products priced between $97 and $297 per month.
Additionally, web publishers have the potential to earn $100 per lead on certain affiliate products, commonly presented as upsells in the customer journey.
With products like One Funnel Away, you get paid $100 which is 100% Commissions.
- Affiliate Sign-Up URL: Clickfunnels affiliate program
- Commission: up to $100
- Cookie: 30 days
Thinkific
Entering the realm of online education could seem daunting.
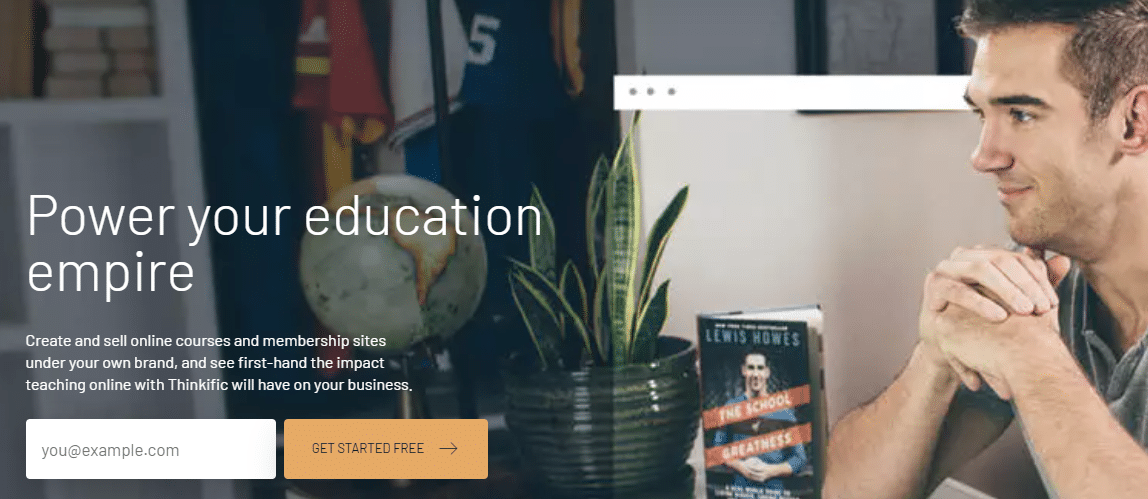 They might contemplate establishing their platform, risking costly errors.
They might contemplate establishing their platform, risking costly errors.
Alternatively, they can leverage online course platforms like Thinkific.
Thinkific empowers average individuals to develop and market their courses while nurturing their learners.
It includes payment processing by default, eliminating the need for coding knowledge.
Thinkific essentially offers a turnkey solution for digital publishing.
As an affiliate, you can earn a 30% monthly recurring lifetime commission for each new Thinkific customer you refer, capped at $1,700 per referral annually.
This program ensures regular monthly payouts, augmenting your affiliate revenue effectively.
It’s a case of selling once and reaping rewards repeatedly.
- URL: Thinkific affiliate program
- Commission: 30% – Up to $1,700/year
- Cookie duration: 90 days
Elementor
Elementor widespread recognition gives it substantial credibility, making it an enticing proposition for affiliate marketers.
Similar to the simplicity of Elementor’s page-building tool, its affiliate program offers straightforward commission rates — a generous 50% of the sales you generate.
 With prices reaching up to $999 per year, the earning potential is substantial.
With prices reaching up to $999 per year, the earning potential is substantial.
- Affiliate Sign-Up URL: Elementor affiliate program
- Commission rate: 50%
- Cookie life: 90 days
Rankmath SEO
 Rank Math SEO is a comprehensive WordPress plugin designed to optimize your website for search engines.
Rank Math SEO is a comprehensive WordPress plugin designed to optimize your website for search engines.
With powerful features and an intuitive interface, Rank Math helps you improve your website’s visibility and drive organic traffic.
Rank Math Content AI helps you write better content in the shortest time.
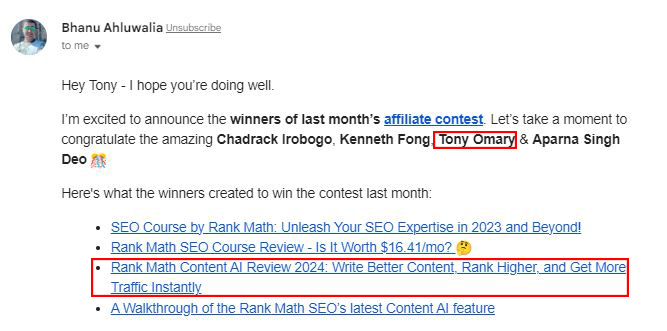
Rank Math organizes an exciting affiliate contest that offers participants the chance to earn additional rewards on top of their regular affiliate commissions.
Affiliates who excel in the contest can earn an extra $200 every month, enhancing their earnings potential beyond the standard commission structure.
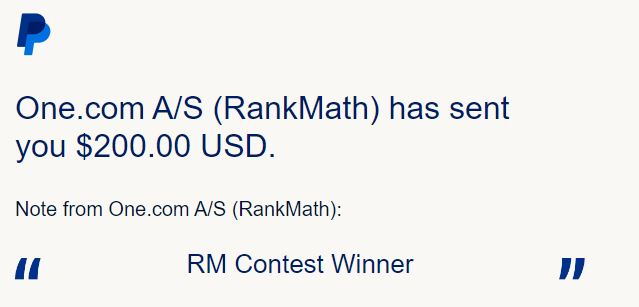 The contest serves as a motivational tool, encouraging affiliates to actively promote Rank Math and drive more conversions while enjoying the prospect of additional rewards.
The contest serves as a motivational tool, encouraging affiliates to actively promote Rank Math and drive more conversions while enjoying the prospect of additional rewards.
- Affiliate Sign-Up URL: Rankmath affiliate program
- Commission rate: 30%
- Cookie life: 90 days
GetResponse
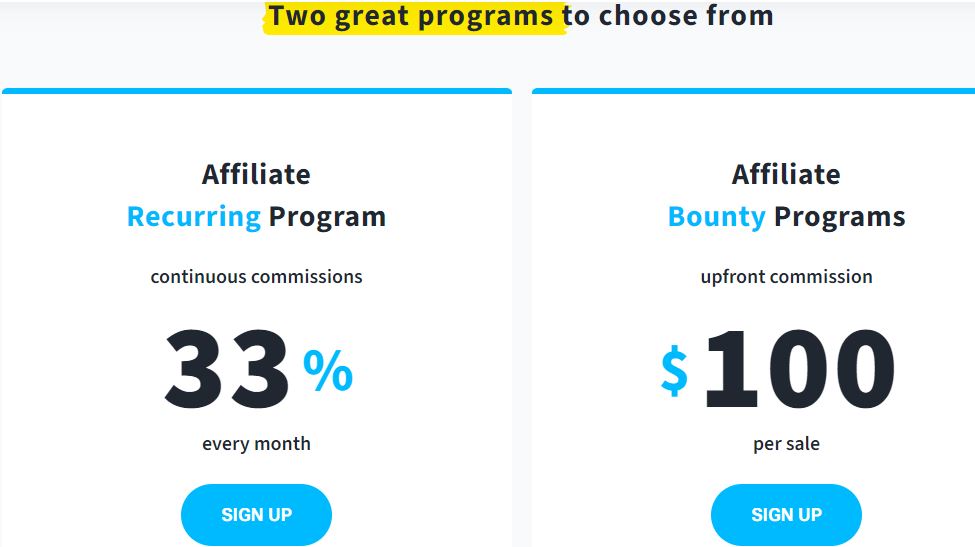 With a focus on rewarding its affiliates generously, GetResponse operates two lucrative affiliate programs.
With a focus on rewarding its affiliates generously, GetResponse operates two lucrative affiliate programs.
One grants a flat $100 commission for each new sale, while the other offers a competitive 33% share of recurring subscription revenue.
Affiliates receive their commissions around the 20th of every month, although the locking period varies depending on the chosen model.
Additionally, to support affiliate success, GetResponse provides access to a dedicated support team and offers valuable business guidance from its affiliate manager.
To join the affiliate program, interested individuals can sign up directly through the GetResponse website or via the CJ Affiliate network.
- URL: GetResponse affiliate program
- Commission rate: 100% or 33% recurring offer
- Cookie duration: 120 days
LeadPages
Leadpages is an intuitive and powerful landing page builder and lead generation platform designed to simplify the process of creating high-converting landing pages without the need for coding skills.
Leadpages offers a no-code, drag-and-drop interface, making it easy for users to create stunning landing pages quickly and efficiently.
Leadpages is trusted by businesses and marketers worldwide for its ease of use, versatility, and ability to drive results in lead generation and conversion optimization.
- URL: LeadPages Affiliate program
- Commission rate: Up to 50% Recurring
- Cookie life: 90 days
Brevo(Formaly Send in Blue)
Joining Brevo’s affiliate program opens doors to lucrative opportunities.
 Earn $5 for every referred user who signs up for a Brevo account, with an additional $100 bonus for every subscription purchase.
Earn $5 for every referred user who signs up for a Brevo account, with an additional $100 bonus for every subscription purchase.
This offer is particularly enticing as it allows you to attract potential customers with a low-commitment incentive, leveraging Brevo’s robust email service to nurture and convert leads effectively.
It’s worth noting that your account validation requires at least one new paid subscription referral, and commission payouts commence post-validation.
- URL: Brevo affiliate program
- Commission rate: $100
- Cookie duration: 90 days
WPX
WPX Hosting is a leading provider of managed WordPress hosting, offering unparalleled speed, reliability, and security for websites.
 WPX Hosting specializes in managed WordPress hosting, ensuring that websites hosted on their platform receive optimized performance and dedicated support.
WPX Hosting specializes in managed WordPress hosting, ensuring that websites hosted on their platform receive optimized performance and dedicated support.
Known as the “World’s Fastest Managed WordPress Hosting,” WPX Hosting prioritizes speed with its high-performance servers and advanced caching technology, ensuring rapid loading times for websites.
WPX Hosting stands out as a reliable choice for WordPress users seeking top-notch performance, security, and ease of use for their websites.
- URL: WPX Affiliate program
- Commission rate: Up to $100
- Cookie life: 90 days
Rocket
Rocket Hosting offers managed WordPress hosting solutions designed to optimize website performance and streamline management for agencies and individuals alike.
 Rocket Hosting boasts a user-friendly interface, making it easy for both technical and non-technical users to navigate and manage their websites effectively.
Rocket Hosting boasts a user-friendly interface, making it easy for both technical and non-technical users to navigate and manage their websites effectively.
Their managed WordPress hosting includes essential features such as free SSL, CDN, WAF (Web Application Firewall), and more, ensuring websites are secure, fast, and reliable.
Rocket Hosting is recognized for its commitment to delivering top-notch performance, security, and ease of use, making it a reliable choice for agencies and individuals seeking high-quality managed WordPress hosting solutions.
Rocket.net offers a special promotion allowing users to sign up for their managed WordPress hosting services for just $1 for the first month.
Despite the discounted price, users still get access to all the features and benefits of Rocket.net’s hosting plans during the trial period.
This includes features such as high-performance servers, automatic scaling, built-in CDN, advanced security measures, and 24/7 support.
- URL: Rocket Affiliate program
- Commission rate: Up to $150
- Cookie life: 90 days
Kinsta
If your blog is flourishing, it may soon surpass the capabilities of your current shared hosting plan, prompting the need for an upgrade.
Enter Kinsta, a leading choice for businesses venturing into managed WordPress hosting.
 Unlike mere promises, Kinsta delivers exceptional performance with lightning-fast load times and unwavering support, ensuring seamless scalability as your business expands.
Unlike mere promises, Kinsta delivers exceptional performance with lightning-fast load times and unwavering support, ensuring seamless scalability as your business expands.
While Kinsta may not be the most budget-friendly option, its excellence compensates for the investment.
It’s a boon, especially considering its affiliate program.
With a commission rate of up to $500 per sale.
Kinsta offers one of the most lucrative payouts in the affiliate realm.
Additionally, affiliates enjoy a 10% monthly recurring commission, providing a steady stream of income for the lifetime of referred customers.
Commission: Up to $500 + recurring monthly commission
Cookie duration: 60 days
Site Ground
SiteGround leads the pack, trusted by over two million domain owners who appreciate its services, evident in its remarkable 99.7% client satisfaction rate.
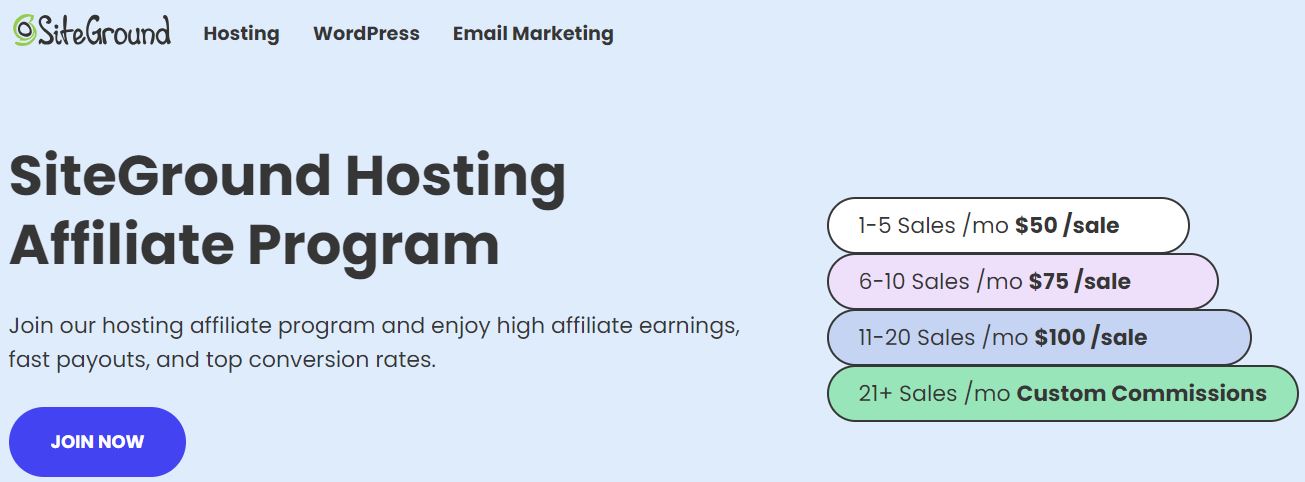 Their affiliate program offers a tiered commission structure, rewarding affiliates with up to €75 per sale based on the number of new signups they generate.
Their affiliate program offers a tiered commission structure, rewarding affiliates with up to €75 per sale based on the number of new signups they generate.
Drive between 11 and 20 new customers monthly to maximize your earnings potential.
Furthermore, SiteGround sweetens the deal by providing new affiliates with a complimentary month of hosting to test their services firsthand.
- URL: SiteGround affiliate program
- Commission rate: Up to €75
- Cookie duration: 60 days
Bluehost
Despite its budget-friendly pricing, Bluehost’s affiliate program remains generous, offering $65 for each referred hosting purchase.
 This opportunity is particularly enticing for affiliate marketers, as evidenced by over $5 million in commissions paid out in the past year alone. Signing up is straightforward, either through the Bluehost website or via Impact.
This opportunity is particularly enticing for affiliate marketers, as evidenced by over $5 million in commissions paid out in the past year alone. Signing up is straightforward, either through the Bluehost website or via Impact.
- URL: Bluehost affiliate program
- Commission rate: $65
- Cookie duration: 60 days
HostGator
Hostgator affiliate program, powered by Impact Radius, features a flexible commission structure.
 Earn $65 for each sale when driving one to five sales monthly, with super affiliates referring 21+ sales enjoying an impressive $125 per sale.
Earn $65 for each sale when driving one to five sales monthly, with super affiliates referring 21+ sales enjoying an impressive $125 per sale.
Despite a payout turnaround of two months + 10 days, aligned with HostGator’s 45-day money-back guarantee, it’s designed to drive clicks on your affiliate links.
- URL: HostGator affiliate program
- Commission rate: Up to $125
- Cookie life: 60 days
Cloudways
 Cloudways emerges as a dynamic web hosting entity, catering to individuals, SMBs, and agencies alike.
Cloudways emerges as a dynamic web hosting entity, catering to individuals, SMBs, and agencies alike.
With a robust portfolio encompassing over 250,000 websites managed proficiently across 60+ data centres, it garners a remarkable customer happiness score of 94.7%.
True to its name, Cloudways specializes in cloud hosting, offering five cutting-edge infrastructures, including Amazon Web Services and Google Cloud Engine.
Its enticing affiliate program sets Cloudways apart, providing affiliates with flexible commission structures.
Opt for earning up to $125 per sale for 46 – 80 monthly sales, with higher rewards for super affiliates exceeding 80 sales monthly.
Alternatively, embrace a $30 base rate alongside a 7% lifetime commission, promising passive income streams.
- URL: Cloudways affiliate program
- Commission rate: Up to $125
- Cookie life: 90 days
Fivver
Aside from its primary service, Fiverr offers supplementary products, including AND.CO, a freelance business management app, and Learn From Fiverr, an educational platform tailored for freelancers and entrepreneurs.
 Affiliate marketers can capitalize on the diverse offerings of this platform, which translates into ample opportunities to earn commissions.
Affiliate marketers can capitalize on the diverse offerings of this platform, which translates into ample opportunities to earn commissions.
Furthermore, Fiverr’s affiliate program stands out with its absence of referral limits and lifetime attribution.
Commissions vary across its offerings, with the Fiverr CPA providing a flexible commission per action, ranging from $15 to $150, based on the service acquired.
Additional commission structures include:
- A generous 50% commission for AND.CO sales
- 30% commission for every course purchased on Learn From Fiverr
- $100 upfront payment plus a 10% revenue share for 12 months on Fiverr Business sales.
Let’s Get this.
- URL: Fiverr affiliate program
- Commission rate: Up to $1,000
- Cookie duration: No referral limit, lifetime attribution
SemRush
A staggering statistic reveals that one in every four Fortune 500 companies relies on Semrush tools, showcasing its widespread adoption and industry influence.
 Given its prominence, it’s no surprise that Semrush’s affiliate program offers enticing commissions:
Given its prominence, it’s no surprise that Semrush’s affiliate program offers enticing commissions:
- $200 for each new subscription
- $10 for every fresh lead generated
- $0.01 for each new signup
Commission payouts occur 27 days after each month’s end, ensuring timely rewards for affiliates.
- URL: SEMrush affiliate program
- Commission rate: Up to $200
- Cookie duration: 120 days
Keap(Formerly Infusionsoft)
Keap stands as a comprehensive solution, amalgamating CRM, sales, and marketing functionalities to empower its users in lead acquisition, conversion optimization, and fostering enhanced customer interactions.
 Recognized by Business News Daily as the foremost CRM for its user-friendly interface and hailed by PCMag as the pinnacle of marketing automation platforms for novice marketers and startups, Keap exudes excellence in its realm.
Recognized by Business News Daily as the foremost CRM for its user-friendly interface and hailed by PCMag as the pinnacle of marketing automation platforms for novice marketers and startups, Keap exudes excellence in its realm.
Yet, Keap’s appeal transcends conventional software utility, as it hosts one of the most enticing affiliate programs in the industry.
Upon successful referral enrollment and a 60-day retention period, affiliates are entitled to:
- $100 commission for Keap Lite referrals.
- $250 commission for Keap Pro and Max referrals. All commissions are disbursed in two monthly billing cycles post the initial purchase by the customer.
- URL: Keap affiliate program
- Commission rate: Up to $250
- Cookie duration: 90 days
Shopify
Shopify is a renowned e-commerce platform powering over one million online retailers across 175 countries, including major brands like Gymshark, Pepsi, and Staples.
 It’s a significant player in the e-commerce industry, facilitating global online retail operations.
It’s a significant player in the e-commerce industry, facilitating global online retail operations.
Affiliate Program Criteria:
To become a Shopify affiliate marketer, you must:
-
- Own and manage an active website.
- Possess an established audience.
- Create original content like online courses, blog posts, videos, or guides.
- Have experience in commerce, entrepreneurship, Shopify, or other e-commerce platforms.
It’s a selective program, not suited for beginners. Build your business first then apply lade when your business has grown.
- Affiliate Sign-Up URL: Shopify affiliate program
- Commission: 200% bounty commission
- Cookie: 30 days
How to Choose the Right High-Paying Affiliate Programs
- Reputation Check: Ensure the affiliate program is reputable and trustworthy by researching reviews and feedback from other affiliates.
- Fit Your Niche: Select programs that align with your niche or target audience. Promoting products relevant to your audience increases the likelihood of conversions.
- Product Familiarity: Choose products or services that you know or have used before. This personal experience allows for more authentic promotion and builds trust with your audience.
- Commission Structure: Analyze the commission structure offered by the affiliate program. Look for programs that offer competitive commissions and bonus incentives for higher sales volumes.
- Earning Potential: Consider the earning potential of the affiliate program. Look for programs with high earning potential per sale or lead, as well as recurring commissions for ongoing income.
- Support and Resources: Assess the level of support and resources provided by the affiliate program. Look for programs that offer marketing materials, training resources, and dedicated support to help you succeed.
Tips for Success with High-Paying Affiliate Programs
- Choose the Right Programs: Select affiliate programs that align with your niche and offer generous commissions for every sale or lead you generate.
- Focus on Value: Provide value to your audience by promoting products or services that genuinely benefit them. Focus on building trust and credibility.
- Niche Specialization: Focus on one niche at a time rather than spreading yourself too thin. Become an authority in your chosen niche to attract a loyal audience.
- Effective Promotion: Implement effective marketing strategies to promote the affiliate products or services. This may include content marketing, SEO, email marketing, and social media promotion.
- Continuous Learning: Stay updated with the latest trends and techniques in affiliate marketing. Continuously educate yourself and adapt your strategies to stay ahead of the competition.
- Negotiate Higher Commissions: Once you’ve proven your value as an affiliate, don’t hesitate to negotiate higher commissions with the brands you promote. Show them the value you bring and how you can contribute to their success.
High Paying Affiliate Programs FAQ
I will do my best to answer common questions.
What are High-Paying Affiliate Programs?
High-paying affiliate programs are programs where affiliates earn substantial commissions for promoting and driving sales of products or services.
These commissions are typically higher than those offered by low-ticket affiliate programs.
How much can I earn from High-Paying Affiliate Programs?
Earnings from high-paying affiliate programs vary depending on factors such as the commission structure, the niche, and the effectiveness of your marketing efforts.
Commissions can range from $20 to $500 or more per sale.
Do High-Paying Affiliate Programs Guarantee Earnings?
No, high-paying affiliate programs do not guarantee earnings. Success in affiliate marketing depends on various factors, including your marketing strategy, audience engagement, and the quality of the products or services you promote.
How can I Succeed in High-Paying Affiliate Programs?
To succeed in high-paying affiliate programs, it’s essential to choose products or services that align with your audience’s interests, create compelling content, and employ effective marketing tactics.
Consistency, perseverance, and continuous learning are also key to success.
Are There Any Sign-up Fees for High-Paying Affiliate Programs?
In most cases, high-paying affiliate programs do not require sign-up fees.
Affiliates can usually join these programs for free and start promoting products or services immediately.
How do I get Started with High-Paying Affiliate Programs?
To get started, research and identify high-paying affiliate programs relevant to your niche.
Visit the program’s website, review its terms and commission structure, and sign up as an affiliate.
Once approved, you can start promoting their products or services and earning commissions.
Conclusion on High Paying Affiliate Programs
High pay does not mean guaranteed earnings.
Here are some benefits and what you need to keep in mind.
- Maximize Earnings: Pursue high-paying affiliate programs to unlock the full potential of your affiliate marketing endeavours. These programs offer substantial commissions that can significantly boost your income.
- Action is Essential: While high-paying programs hold promise, success requires more than just joining. Take massive action, implement effective strategies, and continuously refine your approach to achieve optimal results.
- No Guarantees: Understand that high-paying affiliate programs don’t guarantee earnings. It’s essential to approach them with a realistic mindset, knowing that success depends on your efforts and the value you provide.
- Sign Up and Thrive: Don’t hesitate to sign up for high-ticket affiliate programs. By doing so, you open doors to opportunities for exponential growth and financial success.
- Confidence is Key: Approach your affiliate marketing journey with confidence and professionalism. Believe in your abilities, showcase your expertise, and build trust with your audience. This attitude will set you apart and propel your success in high-paying affiliate programs.
I bet this could be a massive list that cannot be completed in a single writing.
You have the potential to increase your income tenfold by selecting superior affiliate programs and promoting high-ticket items.
However, success also hinges on mastering niche selection and keyword research right from the start.
That’s why Freedom Breakthrough has created free training sessions to guide you in constructing an affiliate site effectively.
If you are ready to pull the Trigger, join Freedom Breakthrough Now and start earning your first high ticket commissions.
Thank you for checking my high-paying affiliate programs for 2026. Which is your favourite?